Index
- Overview
- Updating Statseeker’s Known Hosts
- Disabling Host Key Checking
- SSH Connections after Upgrading your Statseeker Server
Overview
We recommend backing up your Statseeker server on a regular basis, and particularly both pre and post upgrading your Statseeker server. Statseeker offers secure options when connecting to the backup repository – communicating with the backup destination via an ssh or sftp connection. When configuring the secure backup, Statseeker adds a host ‘fingerprint’ for the destination to a ‘known hosts’ file. This fingerprint is then referenced when establishing future connections to confirm that the server Statseeker is connecting to, is the same server that was previously connected to.
- Upgrading the destination server operating system typically results in Statseeker’s locally stored host key fingerprint no longer matching the destination server
- Statseeker’s backup process will fail when attempting to connect to a destination which fails this fingerprint check
To address this situation, either:
- Update Statseeker’s ‘known hosts’ (recommended)
- Disable the host key checking process on the Statseeker server (not recommended)
Updating Statseeker’s Known Hosts (recommended)
After an upgrade to the destination server, a new fingerprint can be added to Statseeker’s known hosts. This is a manual process that will need to be taken after all such changes to the destination server.
- Login to the Statseeker server, and run the following on the CLI
ssh-keyscan -t rsa hostname-or-IP-address
This will return the fingerprint for the specified host.
Example:
ssh-keyscan -t rsa 10.1.2.3 # 10.1.2.3:22 SSH-2.0-OpenSSH_8.8 FreeBSD-20211221 10.1.2.3 ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDbQjwg2hVEoel9Btr9fBbSPbVq0gPw6kXDHJgvomaYL140uHddePnn8J+cF7RVkhg3WWqefFcAw8gSlzHfssJC5MY/IkMmJRwphJ2hCndQFzeiqq59wXo0WpT6yZXnsyplGm5FJ5FNY1ebse/3cPAy2M5atoWZuNcKxN4TBzQ5PqjQwoFxOujOf8kQ/sKEUtrkIAIGdhv2Zi07iUhLDX+SE/Zsz8doTZlSoMMA6ExGe8QTdFvm/PGeGnAgJdwpura95AKN/imN1D/qYcjEir6Rmnv7KuMp8gfDXSXRcGTTsZ/g7UsQrtVTX6otu60ixWxLcGBCsV9/hFLy3OHfb9/2l3udEJjQxYaO4nxYbsfzFgV2FLdaM6MFUSSrmqwqBXi4WpmhePBG1utZyQuY+/5bbEFBUO6YivvdZqhzEKxyVFBIVFQwtM2Pyr+SpnWSW2Fe51qRwAhkbk4mwgQB7J3BQ07j8eBexPC0Nki6KWxlggXiOp+W9HpVERxF/6uGjpM=
Copy the fingerprint and add to the known_hosts file:
- Open known_hosts in the vi editor
vi ~/.ssh/known_hosts
Add the following to the known_hosts:
hostname-or-IP-address ssh-rsa <SSH-fingerprint>
Example:
10.1.2.3 ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDbQjwg2hVEoel9Btr9fBbSPbVq0gPw6kXDHJgvomaYL140uHddePnn8J+cF7RVkhg3WWqefFcAw8gSlzHfssJC5MY/IkMmJRwphJ2hCndQFzeiqq59wXo0WpT6yZXnsyplGm5FJ5FNY1ebse/3cPAy2M5atoWZuNcKxN4TBzQ5PqjQwoFxOujOf8kQ/sKEUtrkIAIGdhv2Zi07iUhLDX+SE/Zsz8doTZlSoMMA6ExGe8QTdFvm/PGeGnAgJdwpura95AKN/imN1D/qYcjEir6Rmnv7KuMp8gfDXSXRcGTTsZ/g7UsQrtVTX6otu60ixWxLcGBCsV9/hFLy3OHfb9/2l3udEJjQxYaO4nxYbsfzFgV2FLdaM6MFUSSrmqwqBXi4WpmhePBG1utZyQuY+/5bbEFBUO6YivvdZqhzEKxyVFBIVFQwtM2Pyr+SpnWSW2Fe51qRwAhkbk4mwgQB7J3BQ07j8eBexPC0Nki6KWxlggXiOp+W9HpVERxF/6uGjpM=
Once known_hosts is open in Vi:
- Type G (upper-case G) – this will position the cursor at the end of the file
- Then o (lower-case o)- to position the cursor at the start of a new line, in edit mode
Add your content, then to save and exit:
- Press Esc to exit edit mode
- Type :x (colon, lower-case x) to save the changes and exit the editor
Disabling Host Key Checking (not recommended)
Another option is to disable the host-key checking process on the Statseeker server. This is not the recommended approach as it may open secure communications between your Statseeker server and other elements of your network to ‘man-in-the-middle’ attacks.
To disable host key checking we need to edit ~/.ssh/config:
- Open config in the vi editor
vi ~/.ssh/config
If this file doesn’t exist on your server, it can be created with:
touch ~/.ssh/config
Disable SSH host key checking for all hosts
Add the following to the config file:
Host * StrictHostKeyChecking no UserKnownHostsFile=/dev/null
Disable SSH host key checking for specific IPs
Host <hostname-or-IP-address-or range> StrictHostKeyChecking no UserKnownHostsFile=/dev/null
Example:
Host 192.168.0.* StrictHostKeyChecking no UserKnownHostsFile=/dev/null
- Save the updated config file
Disabling host key checking will result in warning messages being logged. These messages can be silenced (not recommended) by adding the following to the corresponding section in ~/.ssh/config:
LogLevel ERROR
SSH Connections after Upgrading your Statseeker Server
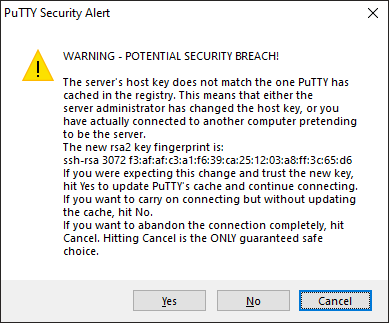
If an operating system update is applied as part of a Statseeker server upgrade, then the server’s host key will change and this will impact users attempting to establish SSH connections to the server.
Typically this change wont cause the connection to fail, but instead will raise a warning advising of the issue and asking for confirmation to update the fingerprint and proceed with the connection.